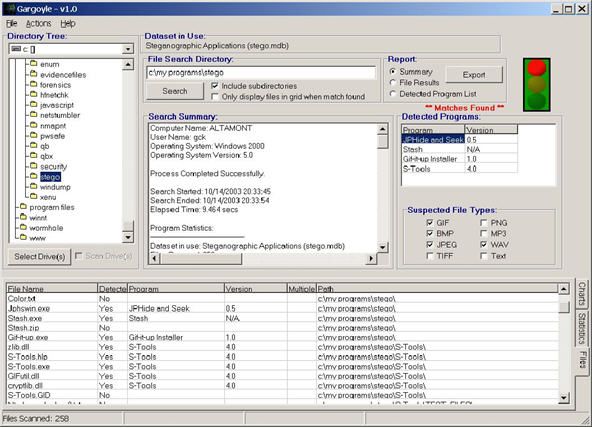
PDF) An Examination on Information Hiding Tools for Steganography | Resul DAŞ and Ismail KARADOGAN - Academia.edu

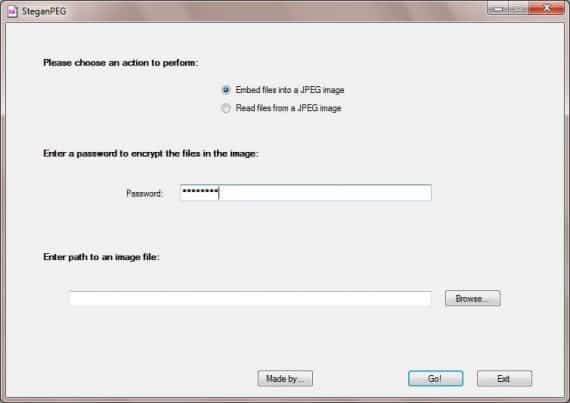
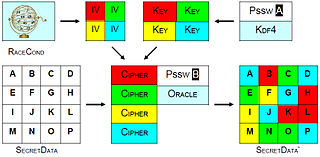
PDF) KHARIM FORENSICS TOOLS AND DATA HIDING TECHNIQUES | MSc Forensics Computing M08CDE: Master Individual Project Project Title: Forensics Tools and Data Hiding Techniques

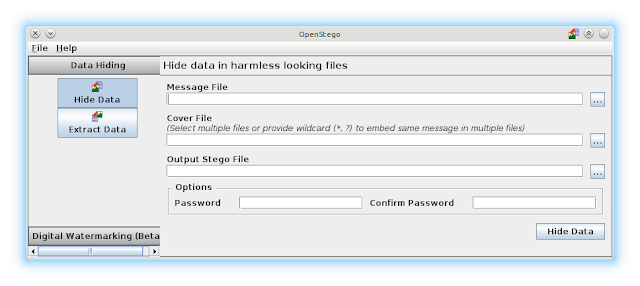
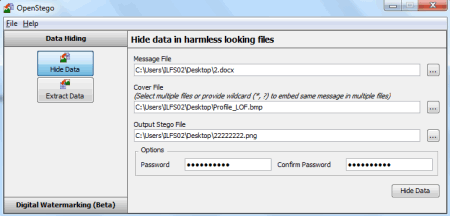
Use of steganographic tools like OpenStego, to detect data hiding or unauthorized file copying - YouTube







![Best tools to perform steganography [updated 2020] | Infosec Resources Best tools to perform steganography [updated 2020] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/2020/10/Steganography04072015.jpg)